Thousands of fundamental industries and a success companies are desperately seeking out certified individuals with CCSK Certification. Knowing the in’s and out’s of cloud protection is a continuously increasing field. People who entire our training often speedy soar into thoroughly paid positions complete of interesting demanding situations and thrilling rewards.
If your enterprise wishes you to get CCSK Certification or you’ve got discovered this training is your maximum direct course to a profitable career in cloud security, we make it wonderful clean a good way to get started out and be successful.
Application Security:
Application safety financial disaster will cognizance software program software improvement and IT companies who want to safely build and set up applications in cloud computing environments, particularly PaaS and IaaS. It consists of some of the techniques used to cozy SaaS packages as properly.
Cloud Computing Architectures:
Cloud Computing architectures will offers the conceptual framework for the relaxation of the CSA steering. It describes and defines cloud computing, units the baseline terminology, and facts the architectural frameworks.

Legal Issues and Contracts Electronic Discovery:
Legal Issues, Contracts and eDiscovery may be covered whilst contracting with CSPs and coping with digital discovery requests in litigation. We will awareness extensively speaking at the criminal implications of the usage of an outside provider corporation.
Information Governance:
How to defend the critical information that powers a client structures and applications. We will cover the way to govern records in cloud computing with new technical protections and new techniques and the way governance specifically influences compliance, privacy, and company regulations.
Governance Enterprise Risk Management:
In Governance and Risk Management, we can popularity on how they exchange in cloud computing area and show off how cloud computing affects regions of governance and risk control; in conjunction with insurance, method, and internal controls.
Virtualization and Containers:
Focus on Cloud computing and virtualization that gives the abstraction needed for useful resource swimming swimming pools and managed the usage of orchestration. Covers all those unique elements of virtualization used to create our beneficial useful resource swimming swimming pools, particularly: Compute, Network, Storage and Containers.
Compliance and Audit Management:
Big attention on the jurisdictional differences and their implications on present compliance and audit standards, approaches, and practices in Cloud Computing. This module covers regulatory environment implications, duties and abilities for demonstrating compliance.
Infrastructure Security:
We will cowl all Infrastructure layers protection which include compute, storage and networking, which additionally embody workload and hybrid cloud. This area includes the basics for private cloud computing. It does no longer encompass all the components of conventional data center safety.
Data Security and Encryption:
Encryption in Cloud and Data safety controls may be covered in three components. In the primary component, we can cover Controlling Data in cloud. Second element will focus on Protecting and Managing Data in cloud. And we will stop with the Access controls, Encryption and Architecture.
Incident Response:
IR in Cloud seeks to find out those gaps pertinent to IR which might be created by means of the precise trends of cloud computing. This may be used this as a reference while growing reaction plans and engaging in extraordinary sports activities throughout the coaching phase of the IR lifecycle.
Security as a Service:
How SecaaS carriers integrate protection competencies as a cloud company. This includes dedicated SecaaS companies, further to abilties from fashionable cloud-computing vendors. We are capable of cowl all SecaaS service to be had and the way they assist at ease a cloud deployment.
Identity and Access Management:
This module awareness on how Identity and Access Management is impacted by using way of cloud computing. In each public and private cloud, events are required to govern IAM without compromising safety. We can even covers how cloud modifications identity management and what to do about it.








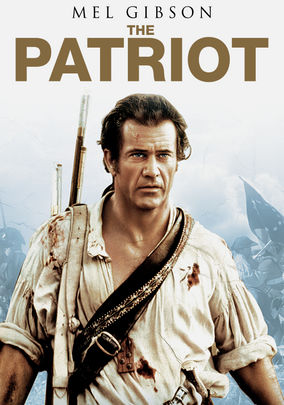 “The Patriot” is decidedly more firmly planted in reality with its entire premise being based on the very-real Revolutionary War and a fictional family destroyed by it. Screenwriter Robert Rodat takes sole credit for this piece and having penned “Saving Private Ryan,” – the greatest film ever made in this critic’s opinion – the similar yet inferior premise is all but marked with his own blood. But don’t think this production foreign to star Mel Gibson either, as the title could well be “Braveheart 2” and few would wince. Unfortunately, the plot is overburdened by Rodat’s apparent need to kill as many people as he can in an attempt to jerk the maximum number of tears possible and to try to add excess depth with a slavery based side plot which serves no purpose other than to overload the film with morals.
“The Patriot” is decidedly more firmly planted in reality with its entire premise being based on the very-real Revolutionary War and a fictional family destroyed by it. Screenwriter Robert Rodat takes sole credit for this piece and having penned “Saving Private Ryan,” – the greatest film ever made in this critic’s opinion – the similar yet inferior premise is all but marked with his own blood. But don’t think this production foreign to star Mel Gibson either, as the title could well be “Braveheart 2” and few would wince. Unfortunately, the plot is overburdened by Rodat’s apparent need to kill as many people as he can in an attempt to jerk the maximum number of tears possible and to try to add excess depth with a slavery based side plot which serves no purpose other than to overload the film with morals.